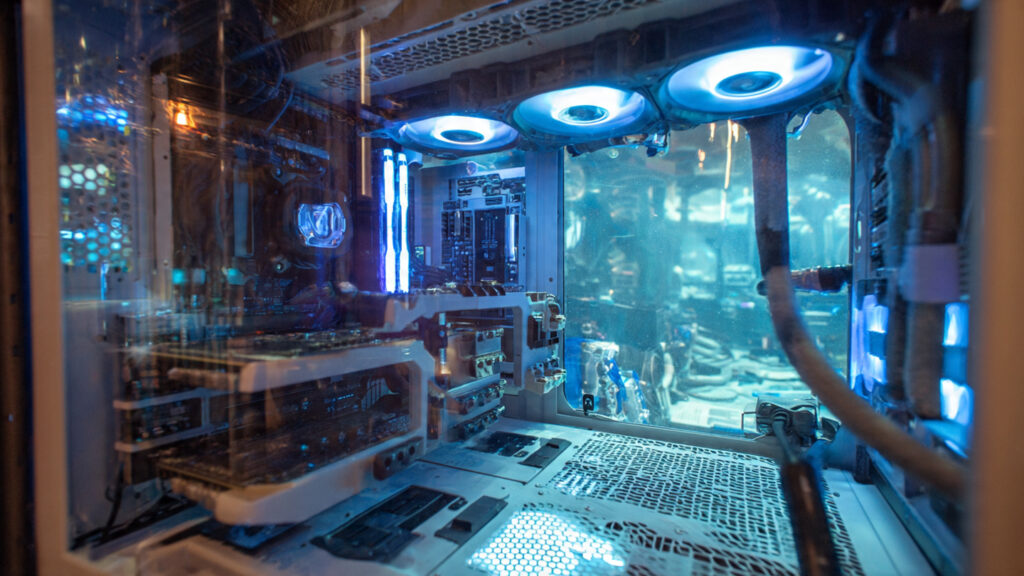
The concept of a personal computer has shifted from a mere consumer appliance to a vital node of individual agency. In an era defined by restrictive software ecosystems and hardware designed to fail within a thirty-six month window, the act of building a machine becomes a quiet rebellion.
We are looking at a landscape where silicon is power. To own your hardware is to own your digital output. This guide rejects flimsy aesthetics in favor of the cyber-industrial standard: a philosophy of over-engineering, thermal dominance, and mechanical permanence.
I | The Philosophy Of The Machine
The shift toward independent command begins with a change in perspective. Most modern hardware is built for the average user who views a computer as a gateway to a handful of streaming services and social platforms. For the high intellect operator, the machine is a high performance engine. It requires an architecture that prioritizes longevity and user serviceability over thinness or portability.
A machine is defined by its ability to remain relevant. This is achieved by selecting components that offer substantial headroom for local artificial intelligence model training and high-fidelity simulation. We want steel, thick copper traces, and oversized heat sinks. We want a machine that feels like a piece of heavy equipment.
II | The Foundation Of Logic And Calculation

The choice of silicon dictates the entire lifecycle of the system. We prioritize platforms that offer socket continuity. Independent command requires a foundation that allows for multiple generations of upgrades on the same board.
In the 2026 landscape, the technical division is stark. Platforms like the AMD AM5 socket have demonstrated systemic integrity by supporting multiple CPU generations, whereas frequent socket transitions in other architectures force unnecessary hardware waste. By selecting a long-term socket, the operator ensures that the workstation remains a persistent node capable of evolution without a total structural overhaul.
We look for architectures that balance high core counts with massive cache reserves. The real performance gains are found in on-chip memory. Large cache pools allow the processor to keep vital data closer to the execution cores, bypassing the latency of the system RAM. This is critical in complex logic tasks where every millisecond of delay is a failure of the interface.
III | Thermal Management As Industrial Design

Heat is the primary agent of silicon degradation. A cyber-industrial build treats cooling as a primary structural element. This means moving away from thin, aesthetic fans and toward high-static pressure units. Liquid cooling must be implemented with caution. We advocate for oversized radiators that provide thermal inertia.
A larger volume of fluid acts as a buffer, allowing the system to maintain a stable temperature even during prolonged high-intellect workloads. For the reliability of air, the dual-tower heatsink remains the gold standard. These massive blocks of aluminum and copper are virtually fail-proof, requiring only a simple fan replacement to last a decade.
IV | The Tactical Memory Array
In 2026, the baseline has shifted. Sixteen gigabytes is a bottleneck. For a machine intended to function as an independent hub, we target thirty-two or sixty-four gigabytes of high-speed memory. This ensures that the system can handle massive datasets and virtual environments without resorting to swap files.
While 16GB is marketed as the business baseline, it offers zero technical headroom for the independent agent. In the 2026 technical landscape, operating systems and background AI-assisted tools consume up to 12GB before a primary simulation is even initialized. By establishing a 32GB or 64GB standard, the operator prevents the system from spilling over into the SSD swap file, a process that introduces mechanical latency and accelerates storage degradation. For those running local Large Language Models (LLMs) or complex persistent world simulations, 64GB is no longer an enthusiast luxury; it is the minimum requirement for systemic integrity.
Latency is just as important as capacity. We look for memory modules with tight timings, prioritizing the speed at which data is retrieved. We favor modules equipped with substantial heat spreaders to prevent memory errors that lead to system instability.
V | GPU Instruction Sets | The Independent Command of the Buffer
The graphics card has evolved into a massive parallel processor. n a cyber-industrial context, we look for cards with excessive video RAM. A card capped at eight or ten gigabytes will find itself obsolete far sooner than one with sixteen or twenty-four.
We prioritize cards with robust power delivery systems. An independent build utilizes dedicated high-wattage cables and avoids flimsy adapters. The cooling solution should occupy three or four expansion slots to ensure fans do not need maximum speed to prevent core melting.
In the 2026 hardware landscape, the independent agent must account for the increasing thermal density of high-performance silicon. Using daisy-chained cables or 12VHPWR adapters is a risk to systemic integrity. We require direct lines of power from the PSU to the PCB to ensure stable voltage regulation under high-intellect simulation loads. Furthermore, the physical volume of a four-slot cooler acts as a thermal buffer, allowing for passive heat dissipation and lowering the acoustic signature of the workstation. This is the technical requirement for a machine that remains a persistent node without mechanical degradation.
VI | The Human Machine Interface

The keyboard is the primary deck from which the user commands the machine. We reject mushy membrane keys. A cyber-industrial deck is built on a heavy steel or aluminum chassis. We advocate for mechanical switches with a clear tactile response.
For the peak of performance, magnetic Hall Effect sensors offer customization and durability that traditional contacts cannot match. These switches have no physical points to wear out, maintaining their feel after ten million keystrokes.
VII | Kinetic Sensors And Precise Navigation

The mouse is the extension of the hand into the digital space. We look for lightweight, structurally sound designs that disappear into the hand. The polling rate is critical. A standard mouse reports its position once every millisecond.
A high-performance industrial sensor can do this eight times as often (8,000 Hz). This reduces input lag to the point where movement feels instantaneous, removing the friction between thought and action.
VIII | Storage Infrastructure And Data Integrity
Your data is the only part of the system that actually matters. We treat storage with a level of paranoia. The operating system resides on high-speed NVMe drives, where the throughput can exceed 10,000 MB/s.
For long-term archives, we utilize secondary storage arrays with built-in redundancy. A properly configured array ensures that if a single drive fails, the data remains intact. This is the foundation of data integrity: knowing your work is protected from hardware failure.
IX | Power Delivery And The Pure Sine Wave
The power supply is the heart of the machine. We demand efficiency and stability. An 80 Plus Platinum or Titanium rating is the baseline. These units waste less energy as heat, improving capacitor longevity.
Beyond the power supply, we advocate for the use of a line-interactive UPS. A UPS acts as a filter, providing a pure sine wave of electricity and protecting the system from surges, brownouts, and total power loss.
X The Display Interface | Reclaiming Independent Command of the Portal
The monitor is the final bottleneck in the system. If the display is tethered to proprietary cloud processing or aggressive automatic brightness limiters, it is not an independent portal but a controlled window. In the 2026 landscape, we identify the monitor as a persistent node that must provide raw, unadulterated data to the operator.
We prioritize hardware that maintains independent command over its own pixel state. This means moving away from traditional LED backlighting that relies on software-driven local dimming and toward self-emissive or high-zone architectures.

For a cyber-industrial build, we look for panels that offer perfect contrast and high refresh rates. OLED technology has redefined what we expect, creating depths of black that standard screens cannot reproduce. Color accuracy is also paramount.
We recommend hardware calibration tools to ensure what you see is an accurate representation of the data. Independent command of the visual field is a requirement for any high-integrity operator. In the 2026 landscape, relying on factory presets or the “eye test” is a failure of systemic integrity.
A calibrated display ensures that the data is not being interpreted by a corporate algorithm but is presented as a neutral reference. We target tools that provide 3D LUT (Look-Up Table) exports, allowing the calibration profile to be loaded directly onto the hardware. This removes the reliance on operating system color management, which is often a source of mechanical latency.
To maintain independent integrity, our hardware audits utilize specific 2026 reference tools. We prioritize sensors that can handle the extreme luminance of modern tandem OLED and micro-LED panels.
- Sensor Thresholds: In 2026, we utilize the SpyderPro or Calibrite Display Plus HL. These devices are rated for up to 12,000 nits, ensuring they do not saturate when measuring the latest high-dynamic-range (HDR) targets.
- NIST-Traceable Accuracy: We discard sensors that do not offer factory re-certification. A tool that has drifted is a tool that compromises the data integrity.
- Ambient Light Management: Real-time monitoring of room light is a requirement. The independent portal must adjust its black point and contrast ratio to compensate for the workspace environment, ensuring the visual proof remains consistent regardless of the sun’s position.
- Content Credentials: Modern calibration software now embeds metadata into the profile. This verifies that the visual output has been audited by a human-led technical process, serving as a signature of independent command.
XI | Audio Fidelity And The Industrial Soundscape
We look for reference-grade audio. This means open-back headphones and external digital-to-analog converters (DACs) that keep audio processing away from the electrical noise inside the PC case.
The goal is transparency. You want to hear exactly what was recorded without artificial coloring. This is the final layer of the high-intellect machine.
XII | The Chassis As A Physical Manifesto

The case is the protective shell. We avoid plastic, opting for thick-gauge steel and tempered glass. The layout must prioritize airflow with mesh panels. Mechanical order is essential.
We choose cases with integrated routing channels for clean, efficient builds. The machine should look as organized as it is powerful.
The Cyber-industrial Technical Matrix 2026
| Component Node | Industrial Specification | Performance Characteristic |
| Central Processor | Ryzen 9 11950X3D or Ultra 9 285K | Multi-layered 3D V-cache with AVX-512 support |
| Logic Board | X970 or Z890 Chipset | PCIe 6.0 integration with server-grade VRM cooling |
| Memory Array | 64GB DDR6 9600MHz CL36 | Dual-channel on-die ECC for bit-flip protection |
| Graphics Core | RTX 6090 48GB GDDR7X | Dedicated tensor architecture for AI-psychology models |
| Primary Storage | 4TB NVMe Gen6 SSD | 20,000MB/s sequential throughput for zero-latency boots |
| Archive Storage | 24TB Enterprise HDD RAID 1 | Mechanical data redundancy for the Property Pantheon |
| Power Plant | 1600W 80 Plus Titanium | Pure sine wave delivery with Japanese capacitors |
| Thermal Solution | 420mm Liquid Metal AIO | High-static pressure turbines for thermal inertia |
| Visual Portal | 32-inch 4K QD-OLED 360Hz | Infinite contrast ratio with Delta E sub-2.0 accuracy |
| Kinetic Sensor | 8000Hz Optical Hall Effect | Zero-debounce magnetic activation for technical precision |
XIV | Why The Cyber-industrial Price Is Justified
The initial investment triggers sticker shock, but we view these figures through the lens of long-term utility. A standard consumer PC lasts three years. A high-integrity machine is designed for a ten-year lifecycle through Socket Continuity and Mechanical Resilience. By investing in the Cyber-industrial Standard, you spend less over a decade while maintaining higher Logic Headroom.
In the collective, time is the only non-renewable resource. High-end hardware is a tax paid for the elimination of friction. Titanium PSUs and ECC Memory protect against grid instability and silent corruption. One catastrophic failure on a cheap system costs more in lost data than the price of this flagship build.
XV| The Network Security Layer
Leaving a high-end machine on a standard ISP connection is a failure of Mechanical Integrity. High-end silicon is a beacon for intrusive tracking. We integrate an encryption layer to ensure safety. For the professional operator, latency is the enemy. We utilize protocols built on a WireGuard backbone, ensuring throughput matches the speed of your Gen6 SSD.
Post-Quantum Resilience is a mandatory standard. By enabling these settings, you are future-proofing your data archives against future decryption attacks. Finally, we utilize Meshnet to link workstations via a private Virtual LAN, allowing for secure file sharing without central server storage.
XVI | The NordLynx Architecture
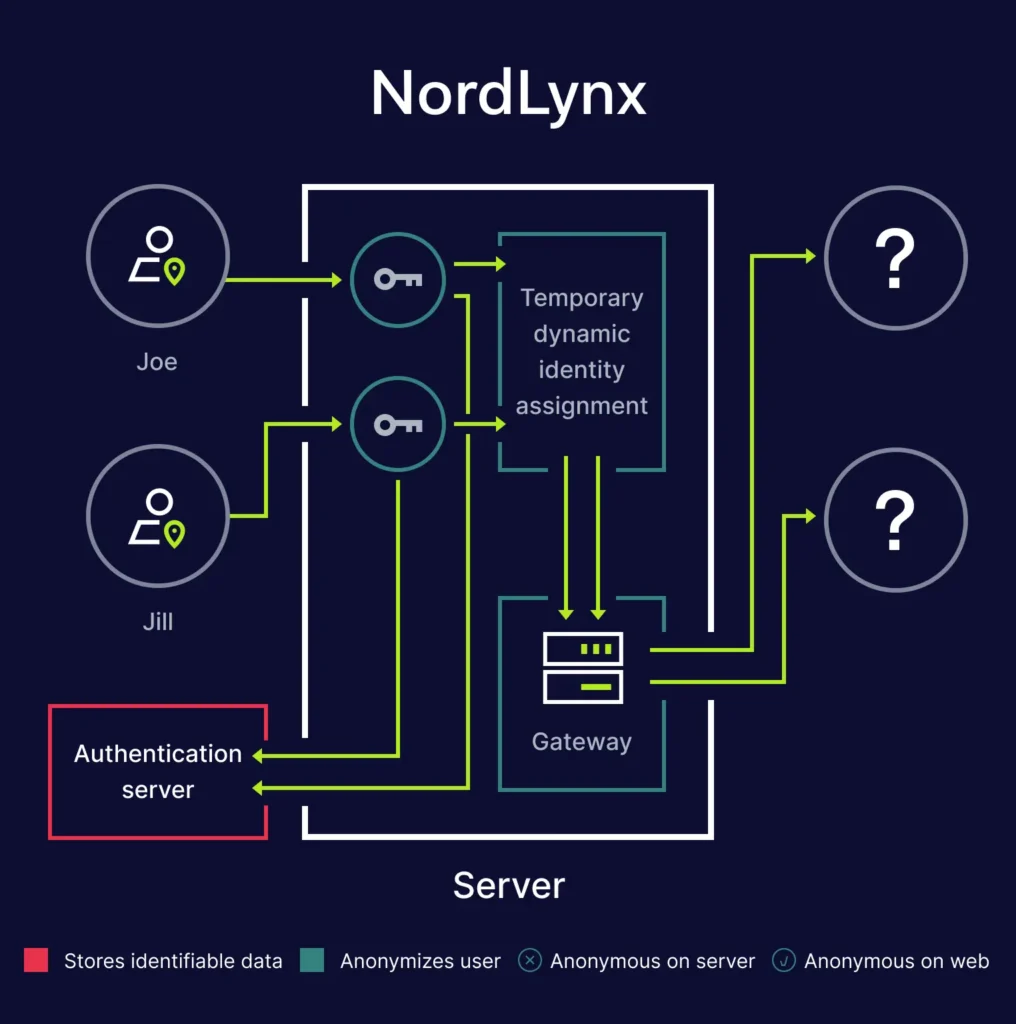
For the professional operator, latency is the only enemy. We utilize the NordLynx protocol because it is built on a custom WireGuard backbone, delivering throughput of up to eight hundred megabits per second with sub twenty millisecond ping. It ensures that the speed of your Gen6 SSD is matched by the speed of your tunnel. Unlike legacy protocols, NordLynx does not throttle your Thread Count or impact frame rates.
XVII | Post-Quantum Resilience
The 2026 grid is already facing the threat of quantum decryption. By enabling Post-Quantum Encryption within the software settings, you are future-proofing your data archives against harvest now and decrypt later attacks. This is a mandatory standard for any machine requiring absolute data integrity. It utilizes a hybrid cryptographic approach that pairs traditional methods with quantum resistant algorithms.
Get the NordVPN 2026 Build Discount
XVIII | Meshnet | The Research Backbone
While many feared its retirement, Meshnet has been preserved and open-sourced for 2026. This allows you to link your workstation with remote nodes via a private and encrypted Virtual LAN. It allows for secure file sharing and remote desktop access without exposing ports to the public grid. It acts as a direct tunnel between devices, bypassing the need for central server storage.
Conclusion | The Tool of the Architect
The shift toward independent command is a commitment to technical excellence. By rejecting disposable culture and embracing the cyber-industrial standard, we create tools built to last. This guide is a roadmap for those who demand more from their machines. We build with resilience, we build with precision, and we build to own our digital future.
In the 2026 landscape, a machine that cannot be serviced or upgraded is a liability. We define hardware persistence as the ability of a workstation to remain relevant across multiple technological cycles. This requires a foundation built on open standards rather than proprietary dead-ends. When the independent agent selects a high-wattage power supply with a ten-year warranty or a motherboard with verified socket longevity, they are not just buying parts. They are securing the infrastructure of their digital estate against the planned obsolescence of the mainstream market.